Business today depends as much on computer security as it does on building security. Unfortunately, it's not as easy to tell when your network is unlocked, as when the front door is wide open.
Your computers take orders and provide information to your customers when you're asleep. You rely on them to store confidential information. You can't afford to lose private customer contact information to a school kid selling credit card numbers on the internet, and you can't afford to have your web site defaced.
We include consideration of security implications as a standard part of every project, and think about it at every step, starting from initial requirements. In addition, each project is reviewed by the team for security implications prior to deployment. We consider secure application design to be a good habit, a developer lifestyle choice -- not an afterthought, and not a document that nobody reads.
Security is not just about technology, but people and process, too. Who needs access to the system we're building? Will they need remote access from home? What happens if the system is compromised? Will the system need to be audited periodically to verify secure configuration settings?
Security is also about trade-offs. At one end of the spectrum, computer security might be a computer in a locked, lead-lined room in the basement of Fort Knox, with no network connection. Well, that might be secure, but the travel, frisking, and background checks required make this a sub-optimal way to provide service to your customers. It normally makes more sense to accept some risk, provide some cost-effective security at multiple layers of the architecture, and have a plan for recovery in the event of a security breech.
illumineX also provides comprehensive security services to government and enterprise customers, including:
Unfortunately, the IT skillsets needed to do security planning, implementation, and auditing are difficult to recruit and retain in today's market, so we are not presently staffed to provide commodity security services to small business customers. However, all of our application development and dynamic web services customers receive the same security review services as our government and enterprise customers.
Our architects have been working with computer & network security architecture and process for over a decade.
What we do…
Why you need it…
How we do it…
Case Studies…
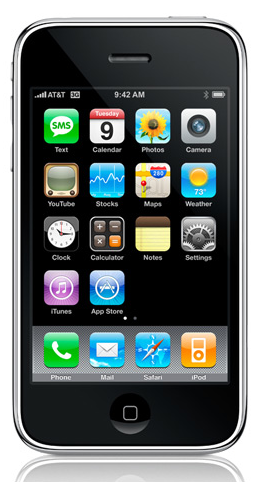
illumineX can help you build iPhone applications for internal enterprise use, or for consumer use.